The
Woman Who Smashed Codes - Jason Fagone
The
Third Reich Is Listening: Inside German Codebreaking
1939-45 - Christian Jennings
Already in the 1924, cryptanalyst Wilhelm Fenner was one of the leading figures in the German cipher bureau, later known as Pers-Z, which focused on the crypto systems of foreign armies. In 1923, Wilhelm Tranow, a navy cryptanalysis veteran became one of the leading figures in the naval intelligence agency, called B-Dienst, which proved very successful in breaking the British naval communications. In the runup to WW2, German signals intelligence grew steadily into a plethora of different agencies. They all competed to recruit the best cryptanalysts, but were also plagued by distrust, especially the Reich Security Main Office or RSHA, overseen by Himmler’s SS. At the beginning of WW2, Fenner became director of OKW-Chi, the Cipher Department of the Wehrmacht, and Erich Hüttenhain and astronomer Walter Fricke the leading cryptanalysts in the cipher bureau of the OKH, the Army Command. Throughout the Second World War, the B-Dienst continued to break the British naval ciphers, used by convoy escorts and merchant ships. At the start of the war, the Luftwaffe Command cipher bureau OKL-Chi was able to break British air force communications and OKL-Chi signals intelligence units revealed the composition of British squadrons. This however did not prevent the German defeat by the RAF in the Battle of Britain. The Luftwaffe codebreakers also had important successes in Russia. But once the Allies opened a second front with the Mediterranean campaign, the Germans had to fight on two fronts. As of then, their signals intelligence units were in a constant withdrawal, decreasing their capabilities and successes. Likewise, although successful in breaking British naval codes, the breaking of the Kriegsmarine Enigma and reading the U-boat communications turned the tide in favor of the Allies. In the end, Germany lost the signals intelligence battle, despite having excellent codebreaker and well-organized cipher bureaus. The constant bureaucratic battles, too many different agencies, each wanting its share, the difficulties to recruit and keep experienced people when the war progressed, and the meddling and distrust of the various security agencies and their heads took its toll. The book is an excellent and very
detailed account of the German codebreaking and signals
agencies, how the services were formed, the quite capable
personnel and how they failed. Jenning's book is a
well-researched reference book that finally sheds a light
on German signals intelligence during the Second World
War. As introduction to the book, you can listen to History Hack's German
Code-Breaking in WW2 The Third Reich Is
Listening The Billion Dollar Spy - David
E. Hoffman In January
1977, CIA chief of station Robert Fuller was filling up
his car at a gas station in Moscow when a Russian man
approached him, asked to talk with him and immediately
dropped a note on Fuller's car seat. In the note he
explained that he wanted to discuss strictly confidential
matters with a U.S. official and proposed to arrange a
meeting. Fuller reported the contact to CIA headquarters.
They feared that the man was a dangle, a trap by the KGB
to expose CIA operatives. Fuller was instructed to ignore
the man. The Russian man however persisted. He made two more attempts in February, each time dropping a note, proposing a signal and meeting. After being ignored again in May, it seemed that the KGB gave up the dangle. That summer, Gus Hathaway succeeded Fuller as chief of station Moscow. On December 10, the Russian man spotted a car with embassy license plate, approached the driver and urged him to deliver his letter to a U.S. official. In that letter, delivered to Hathaway, the mysterious man explained that he had access to research into look-down radar and that he could also provide schematics for the new MiG-25 radar. This information finally tickled CIA headquarters' interest. They assigned the codename CKSPHERE to the Russian man but did not find him worth the risk of exposing a CIA operations officer. Hathaway, by then convinced that CKSPHERE was most likely an engineer at a secret research laboratory, insisted on meeting the man. CIA however again ordered Hathaway to ignore the requests for a meeting. On February 16, 1978, more than a year after the first contact, CKSPHERE again dropped a note, this time in Hathaway's car. By then, the man was desperate but afraid to reveal more personal information. Meanwhile, the Pentagon expressed to the CIA their great interest in Soviet aircraft electronics and radar. On March 1, the Russian man once again approached Hathaway, who was just unlocking his car, and pushed a packet into Hathaway's hand. It contained all the personal details that convinced the station chief and the CIA that he was a genuine spy. CKSPHERE now had a name. Adolf Tolkachev, engineer and leading designer at the Scientific Research Institute for Radio Engineering in Moscow, and he resented the Soviet system. The next seven years, Tolkachev provided a tremendous amount of highly sensitive information on Soviet research related to aircraft electronics, radar and weapons systems. For Tolkachav it was a race against the clock. He knew that his game would eventually end and therefore tried to pass as much information as possible, often taking great risks with disregard for his own safety and despite his case officers urging him to be cautious. In the end, his information saved the Pentagon and the U.S. Air Force billions of dollars in research and development and made sure the West had a critical technological and military advantage over the Soviets. The Billion Dollar Spy, researched and written by David Hoffman, brings Tolkachev's story, based on declassified documents and many interviews with the CIA personnel involved in the CKSPHERE case. Hoffman's extensive research resulted in a highly detailed account that isn't limited to the spy story itself but also provides a better understanding in how the CIA handled the case, the events that lead to the fall of CKSPHERE and consequent fall-out, all placed in the broader context. The book offers a fascinating insight in the modus operandi of CIA station Moscow. It details the tricks of the spy trade, how the case officers set up meetings and performed surveillance detection runs, the various ways they communicated covertly with Tolkachev, and the spy gear the CIA developed and provided him over the course of eight years. The reader learns in detail how they ran such operations in Moscow station. The book truly excels in the details and background information on the characters involved. You get to know Adolf Tolkachev through the many operations notes and letters with personal information he wrote to his handlers, and you discover the reasons why he became so resentful against the Soviet state. Tolkachev was a complex man. He was intelligent and wanted to do things his way. He declined the proposed use of dead drops or a spy radio. They gave him a SRAC (short range agent communications) to send messages by burst-transmission, and later even provided him with a novel satellite message system, but he never used them. He preferred meetings in person, despite the according risks. CIA gave him the most advanced spy cameras, but he insisted to use his own Pentax camera. He regarded money as a token of respect, rather than a means to get rich, but complained each time when he received too little money for what he believed to deserve. His fear for getting caught alive contradicted with the ever-increasing risks he willingly took. He therefore was worried about his wife and son but had already decided he would never leave Russia. There were also the little things. He often asked his handlers for music records from western bands, books or ink pens and gums for his son. Hoffmann explains why the CIA, paralyzed by James Angleton's paranoia in the 1950s and 60s, was so reluctant to set up operations in Moscow, the frustration of Gus Hathaway with CIA headquarters and his efforts to protect the man behind the source. Tolkachev's case officers, John Guilsher, David Rolph and Bill Plunkert had to operate and arrange face to face meetings despite overwhelming KGB surveillance. The meetings later became so risky that CIA decided to use Robert Morris, a deep cover, to meet Tolkachev. You can't get it more exciting. The reader gets plenty of background information to understand how the CIA handled the cased. Hoffman also delves into the history of other spies, like GRU Colonel Oleg Penkovsky (HERO and YOGA), and Soviet diplomat Alexander Ogorodnik (TRIGON), and tells the stories of Marti Peterson, the first female CIA operations officer in Moscow and the exfiltration of KGB Major Victor Sheymov by David Rolph. Many more relevant people from the intelligence community are given a place in the book. The fall of CKSPHERE is credited to Edward Lee Howard, a former CIA officer in training who was assigned to Moscow station but was fired before his departure to Moscow. He offered his services and all his knowledge about Moscow station to the Soviets. His downfall is also written down in this very comprehensive book that reads like a spy thriller. If you like to know the real deal, this well researched book is it. The Billion Dollar Spy The
Codebreakers: The Comprehensive History of Secret
Communication from Ancient Times to the Internet - David
Kahn
Giving a summary of the book is almost impossible, considering the huge wealth of information. The first chapter starts in 1941 and describes chronologically the events leading up to the attack on Pearl Harbor, and the work of OP-20-G, the U.S. Navy’s cryptologic organization. This 70 page introduction immediately makes clear what cryptography is about, and how it influences history. This gripping first chapter puts you in the front seat of history and makes you want to ride straight through Kahn’s massive 1000-pager. The story of cryptology starts in 2000 B.C. and the book traces its origins, from the first hieroglyphs, over the early Arabic work on cryptanalysis to the Middle Ages. Western civilization would have to wait until the 14th century before secret writing gradually developed in the hands of people like di Lavinde, Soro and Porta, and the first book on cryptography, Trithemius’ Polygaphyiae. Kahn brings alive the stories from monks, popes, kings, espionage and treason, and he explains how all the classical ciphers work and how they were broken. In the 17th century, codebreaking became a powerful tool in the hands of people like Antoine Rossignol and John Wallis. The era of the black chambers, how they worked, their achievements, decrypting communications from friend and foe to assist politics and diplomacy, it’s all there. Various nomenclatures, codebooks and ciphers are presented. Cryptology moved from a mysterious dark art to real science in the 19th century. The invention of telegraphy evoked an explosion of communications. Jefferson, Wheatstone, and Babbage, the American Civil War and conflicts in Europe lead to the invention of many so-called field ciphers, extensively used by the military. Auguste Kerckhoffs, Etienne Bazieres and many others contributed to the mechanization of cryptography by writing books or inventing crypto machines. The many conflicts in the early 1900’s showed the need for specialized military organizations, not only to implement cryptographic systems, but also to intercept and decipher enemy communications. Radio communications became widespread and so did the commercial market of crypto machines. The war of intercepts had started. Kahn describes in detail cipher systems, how and where they performed on the battlefields during World War I, and how the United States finally catches up with the European continent, thanks to people like Herbert Yardley and William Friedman. During the Second World War, cryptanalysis finally evolved from raw intelligence into a vital part of modern warfare. Examples are innumerable, and Kahn does a wonderful job in bringing alive the many war episodes that were determined by the making and breaking of codes. Signals intelligence kept playing a major role during the Cold War, and Kahn devotes a complete chapter on Russian cryptology, returning to its origins in the 18th century and explains how they developed into a key player the Cold War, with the according espionage stories. The history and work of NSA (National Security Agency) is followed by the anatomy of cryptology, and a detour to the use of ciphers and codes by the American rum runners during the prohibition years, gamblers and businessman. Kahn also peeks into the past, with the deciphering of ancient languages, and briefly peeks into the future with communications with outer space. The book was published in 1967 and therefore did not contain any recently declassified information about, for instance, the breaking of the German Enigma machine, the expansion from cryptography into the public domain, the Internet or the evolution of signals intelligence. The 1996 edition contains an additional 15-page short chapter which merely touches these subjects. However, given the many detailed books, published today about these more recent, there is no need for an extensive revision of the book. With 27 chapters and 1180 pages (of which 194 pages notes and references) the book is already a massive read. Although the book also presents some classical cryptologic techniques, it is not a technical work for cryptologists or mathematicians. David Kahn’s The Codebreakers is a unique one-in-a-kind reference on the history of cryptology with numerous exciting stories that will captivate even those who never heard of cryptology. Highly recommended! The Codebreakers
Nuking the Moon: And Other Intelligence
Schemes and Military Plots Left on the Drawing Board -
Vince Houghton
Deep Undercover:
My Secret Life and Tangled Allegiances as a KGB Spy in
America - Jack Barsky Imagine driving on the interstate on a Friday
evening with a great weekend ahead. You just passed the
tollgates, and a state trooper waves you over. The moment
you get out of the car, an FBI agent approaches and tells
you he would like to talk to you. You and I would wonder
what on earth the FBI wants from you. Jack Barsky
didn’t wonder. He knew his life would never be the
same anymore. If you dream of joining the secret service and operate as an illegal agent in foreign countries, you better think twice. It is indeed fascinating work but there's little glory or 007 excitement. Only lots of stress and worries. Ask Jack Barsky, formerly known as Albrecht Dittrich. In 1970, Albrecht Dittrich was a talented student at the university of Jena with a promising career in chemistry until a knock on his dorm room changed the course of his life. Scouted by the Stasi, Albrecht was asked by the KGB to join the almighty Soviet secret service and defend the communist ideals as a secret agent. And honestly, you and I would have been honored to do just the same in similar circumstances. This book explains the how and why. Albrecht grew up during the harsh post-war years in East-Germany. As a brilliant student he was destined to join the league of men who would define the future of his country and socialism. His childhood shaped his character and ideals, and when offered to serve the socialist cause in the secret service he eagerly took the challenge. They called it serving but in reality, it meant sacrifice. He left family, friends and love to be trained in Moscow as illegal agent. He told his mother he worked in diplomacy and many loved ones were told other fake stories in the next decades. Serving as illegal non-registered agent of the KGB in the United States - the main adversary - is arguable the highest rated mission in intelligence work and more a calling than work, but it had its downsides. In 1978, after extensive training in secret communications, counter-surveillance, English language and learning his new identity, Albrecht Dittrich finally arrived in the U.S. to shake off his past life and start a new one as Jack Barsky. It was a formidable task to go from zero to hero. His book gives an excellent insight into what it takes to establish a new identity, acquire a fictitious but credible past and the trouble to transfer that fiction onto genuine official documents. It’s an account of many tricks of the intelligence trade, learning to adapt to the culture and particular habits of an unknown country, getting a university degree all over again, loneliness, the pressure of evading counter-intelligence, improvising solutions to problems that the KGB didn't take into account, missing his wife and child and eventually alienate from his loved ones. Despite the challenges, Jack Barsky managed to live the American but fictitious Dream and rose from bicycle messenger to successful manager in a large software firm. At the same time, he was challenged in a way that every illegal agent has to cope with. As he began to appreciate the opportunities, given to him by the United States, his dedication to the communist cause faded and he reluctantly decrypted his weekly received radiograms with instructions from KGB headquarters. Eventually, he fell in love and married a woman in the U.S. but his double life took a toll on his marriage. And just when his covert life finally seemed to have embedded perfectly in the land of the main adversary, he was waved aside at that tollgate. The book is a real page-turner. How Albrecht Dittrich was made a spy, his training, how he embedded as Jack Barsky, what ended his spying career, how he was finally caught and his surprising redemption. But the book doesn't merely provide a fascinating account of espionage tradecraft. It's also a very personal story about the psychological and emotional burden of living a covert life. It unravels the reasons why a self-confident and a bit arrogant young man becomes a dedicated spy who sacrifices his real life in exchange for a fictitious one, how it is to even lose that fabricated life and how he eventually finds a new purpose in life. You cannot but imagine how you would feel when you had to choose between loyalty to your country, wife and children, cope with building a new future in a country far away and then see everything falling apart. Could you live that covert life, knowing that it can all be over in a blink of an eye? More about Jack Barsky on SIGINT CHATTER Deep Undercover Secret
Power: New Zealand’s Role in the International Spy
Network - Nicky Hager
The book provides many details about the origins and history of the New Zealand Government Communications Security Bureau (GCSB), their collaboration with the other SIGINT agencies and the how and why of the most secretive UKUSA agreement. In the 1980s, a system was introduced to automatically categorize, filter and store the vast amount of intercepted signals from commercial satellites, radio communications, telephone, fax, Telex and e-mail traffic. The system, codenamed ECHELON became an enormous source of intelligence. Although apparently a child of the Cold War, ECHELON does much more than protecting the participating countries against the - meanwhile perished - Soviet Union or safeguarding their nations interests. It enables massive eavesdropping on both enemies and friends, and for many years, this was done without consent or knowledge of the New Zealand parliament. ECHELON was so secret that only the GCSB staff knew - more or less - what they were doing. Moreover, the technology, training and key staff members were provided by the American NSA and the British GCHQ, the UKUSA key members. ECHELON is based on software, called Dictionary, to filter potential interesting information with the help of key words. The five countries can individually compose and adjust different key word tables to filter out the intelligence they need. ECHELON also interconnects all the listening stations, located across the world. All five countries harvest intelligence and - theoretically - profit of the remote spy stations of their fellow eavesdroppers. However, the 'return on investment' for junior members Australia, Canada and New Zealand is nothing compared to their British GCHQ counterpart and especially the NSA, the agency that designed and fully controls the ECHELON system and its Dictionary. At the end, New Zealand embarked on a Big Brother project without being aware of what ECHELON was used for, what information the key players filtered out the GCSB stations, and without having any democratic control over this most secret operation. The information in the book is based many years of painstakingly puzzling together the very scarce information, tracking involved personnel and interviews with staff members of the GCSB. A quest that started in 1984 and lasted until the 1996 publishing of the book. The result is a detailed report on how the spy network and ECHELON are working, who is targeted and what information they harvest. Hager's investigations provide an insight view, not only in GCSB's kitchen, but also in the GCHQ, the NSA and the Australian DSD. A truly fascinating book! The e-book version (pdf) is now on-line
available and free to download at Nicky Hager's website Station
X: Decoding Nazi Secrets - Michael Smith
The Enigma cipher machine was used in
all parts of the German Army, Luftwaffe and Kriegsmarine.
Breaking this code could turn the tide of the war. This
book is the story of the people who broke the code, how
the codebreaking was organized, and gives us a pretty
good idea of how people lived in Bletchley Park. Breaking
Enigma played a decisive role in many parts of the war
such as the Atlantic, Africa and D-day, and shortened the
war by several years. The
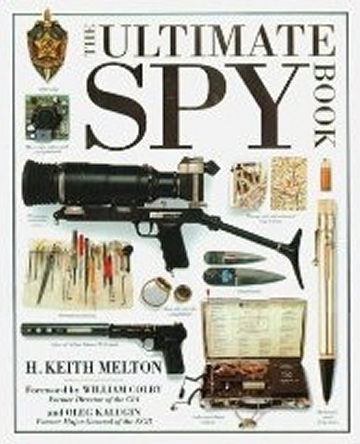
Ultimate Spy Book - H. Keith Melton
However, a major part of the book is, not surprisingly, about the Cold War. The Cold War was a period in history that was characterized by mistrust and fear between East and West. These were the heydays of espionage, with Berlin as the capital of spies. Many of the most notorious spy cases were about the battle for intelligence information between the United States and the Soviet Union during the Cold War. This battle was fought in the sky, with U2 spy planes and satellites, but also on the ground by intelligence officers and their agents in enemy territory. Hidden and automatic cameras for observation such as the Robot Star, small mini cameras like the famous Minox or the F21 with its lens in a jacket button for clandestine photography and small camera systems to copy documents. You will discover communications equipment for covert operations, monitoring equipment and dead drops to secretly pass documents and films. Melton also brings us the story of secret operations and the special devices that were developed for these operations. If there are spies, there's counterintelligence. Bug detectors, anti-eavesdropping equipment, interception of documents and all kind of tools to burgle or secretly gain access to installations or documents of the enemy. Training and recruitment, spy rings, false covers and legends, it's all there. But above all, The Ultimate Spy is a book to watch, with many splendid photos about the art of spy-craft and its technology. A book that would make James Bond's Mister Q jealous. The Ultimate Spy Book Man
Without A Face / Die Trojka / Im eigener Auftrag - Markus
Wolf
In 1953, he was one of the founding members of the foreign intelligence service, a department of the ministry of state security, also called Stasi. As head of the HVA, Wolf developed the most effective secret service of the Cold War. After retiring in 1986, he wrote a book which was originally a film project of his late brother Konrad, about Konrad and two friends, growing up in Moscow in the 1930s. Konrad joined the Soviet Army, one friend joined the German Luftwaffe, and the third one joined the US forces. After the war, the three friends meet again and keep in contact. The book, Die Troika, a statement for friendship which also exposed the failure of communism, was published in East and West Germany. For the people in the East, Wolf, who supported Glasnost and Perestroika, became a symbol of the ongoing changes in a country that rejected the changes in Eastern Europe. Although Wolf headed only the foreign intelligence, one of many departments of Erich Mielke's Stasi, he became targeted as Stasi spy chief by the media during the period of the fall of the Berlin Wall. After the collapse of the German Democratic Republic Wolf was charged and sentenced for espionage, bribery and treason in the reunified Germany, but that conviction was later overturned, and he received a suspended sentence on lesser charges. In the book The Man Without a Face Philby:
KGB Master Spy - Phillip Knightley
His main objective was to infiltrate the SIS. He went to Spain as newspaper reporter and pretended to be a supporter of the fascist General Franco, to erase his communist past. In 1940 he was recruited by the SIS after recommendation by the already infiltrated Burgess and one year later he worked at the counter-espionage branch. By the end of 1944, at the dawn of the Cold War, he had been promoted to head of counter-espionage and anti-communist operations. Five years later he was promoted to the SIS top function in Washington which gave him access to US operations against the Soviet-Union, the top secret VENONA project, and other sensitive information. After the defection of his close friends Burgess and Maclean to Moscow, he came under suspicion with MI5 and got fired. Due to lack of evidence his name was cleared and by 1956 he was covertly recruited again by the SIS as agent in Beirut. After the defection of KGB agent Golitsyn his treason was exposed, and the SIS proposed exemption of prosecution in exchange of a full confession. However, early in 1963 Philby vanished in Lebanon to surface a few weeks later in Moscow, where he was received as a hero. The performance of this master spy is unique and for almost 30 years caused enormous damage in the hart of the battle against Soviet Intelligence. This book is based on many interviews with Philby himself in Moscow and has been verified by historical research. KGB Master Spy Loyal
Comrades, Ruthless Killers: The Secret Service of the
USSR 1920s to the Present - Slava Katamidze
Katamidze doesn't hide his criticism on the secret services and their violent history. Many of the most notorious spy cases and KGB intelligence successes are described and you can find details about nearly all high ranked people in the secret service, all of this illustrated with many unique images. Having said this, I also have some serious questions about this book. Although a very good introduction, it fails to go into detail on several important episodes in the history of the Soviet Union and its secret service. The author presents some new and questionable facts about names and numbers, criticizes some people and is striking mild on others. The book regretfully lacks the sources for these new facts, giving the book a sense of subjectivity, although it's hard to tell in which direction. Slava Katamidze has a background as officer in the Soviet Army, studied at the institute for foreign languages and institute for international law in Moscow. Sounds like a perfect candidate for the GRU (military intelligence, known for its fierce rivalry with the KGB). Although nowhere mentioned and only an educated guess of mine, it would explanation the duality of the book in its criticism on the secret service and at the same time forgetting some dark Soviet episodes and details. Nonetheless a fascinating introduction and beautiful illustrated book. However, I recommend reading books such as The Mitrokhin Archive after this one, to get another view on the story. Loyal Comrads, Ruthless
Killers Chatter:
Dispatches from the secret world of global eavesdropping
- Patrick Radden Keefe
The
Sword and The Shield: The Mitrokhin Archive - Christopher
Andrew & Vasili Mitrokhin
In 1992, he walked into a British embassy in a Baltic state and by the end of that year he was exfiltrated by British Secret Service, together with several large crates of documents. The consequences were devastating for the KGB. Details about secret operations and the names and code names of Soviet spies came into the hands of intelligence services in the West. As the facts got published, SVR, the successor to the KGB, replied that it was simply impossible that hundreds of names could be exposed, 'in worst case a few'. The reality was that more than one
thousand names were revealed. This enabled secret
services to identify or catch many Soviet spies. This
large book contains an enormous amount of information on
the history of the secret services in the Soviet Union
and detailed info on Soviet spies and numerous secret
operations. The
Code Book: The Science of Secrecy from Ancient Egypt to
Quantum Cryptography - Simon Singh
Without going into technical details, he shows the importance of cryptology in politics and war over many centuries. We read how cryptography was developed as an important weapon against Signal Intelligence, and the role of codebreakers in SIGINT. In this age of technology, internet and communication, Singh explains the importance of encryption to protect our privacy. This isn't a detailed book aimed at
crypto geeks, but a good introduction to cryptography
with some basics on classical encryption methods and a
bit of theory on modern algorithms like RSA. This book is
a must for those who think that encryption isn't
important. The
Game of The Foxes - Ladislas Farago
The book explains how the Abwehr was formed, how Admiral Canaris developed it into an effective secret service, and his struggle with the other German security services. We can read about the preparations for war and the invasion of Poland, as well as the spy networks in England, the success of the British counterintelligence and the Double-Cross system that turned virtually all German agents in England into double agents. There's a large chapter on pre-war industrial and military espionage and sabotage by German spy networks in the US. You can read how the Abwehr tried to influence US elections and prevent a third term for F. D. Roosevelt, who was in favor of military support for Europe. The archives reveal the misplaced confidence in the Abwehr agents operating in the US, and how the FBI eliminated most of the spy networks once the US entered the war. The archives show the infiltration of foreign embassies, the spy network in neutral Sweden and the support for General Franco in Spain. In 1944 the Abwehr finally lost all credit with the Nazi top brass, in favor of Schellenbergs Sicherheidsdienst Ausland, and Admiral Canaris was forced to leave the service. The Allied success of operation Fortitude, to mislead German intelligence about the invasion on D-Day, was the last major battle between the secret services and finally lead to the fall of the Nazi empire. The question remains in how far Canaris, who became anti-Nazi, was responsible for the failure of his intelligence service and the outcome of war. The Abwehr, by then under command of the RSHA, soon collapsed without the expertise of Canaris who was executed later by the SS in Kamp Flossenburg for conspiracy against Hitler. This detailed story of the recovered Abwehr archive is a unique piece of WW2 intelligence history. The Game of The Foxes IBM
and the Holocaust: The Strategic Alliance between Nazi
Germany and America's Most Powerful Corporation - Edwin
Black
When Thomas Watson became president of IBM, his goal was to expand the company on a global scale, regardless any political, military or ethic obstacle. A crucial player in the organization of the Holocaust was Dehomag, a German sub-company of IBM. The Hollerith machines, the predecessor of the computer, were able to perform statistical calculations and organize data with an unmatched speed. Already in the early 1930s the Nazis placed large orders at Dehomag to organize their industry, finances, railways but also to automate the identification of Jews. All Hollerith machines had to be customized for each specific task and special punch cards were designed to store detailed information. Although the Germany based Demohag company officially processed these orders, it were the IBM engineers who controlled the complete process, and all financial decisions were made by IBM New York and its executives. Even when Jews were openly prosecuted and deported, even when war broke out, even when all trade with Germany became illegal, IBM continued to produce and lease Hollerith machines, developed custom solutions for the Nazis, offered maintenance and gained massive profits of this, of course hidden in a labyrinth of confusing financial and legal tricks. Given the complex requirements to develop specific custom solutions, which included detailed data input and question lists, IBM was well aware of the purpose of the ordered machines. Moreover, IBM was constantly involved in legal battles to obtain more and more profit of its successful sub-company Dehomag. Meanwhile, Hollerith machines produced precise address lists of Jews in Germany and many occupied countries, organized their deportation and enslaved labor, enabled smooth railway timetables to transport millions of people across Europe and boosted the efficiency of the German war industry. IBM was the one who leased the machines and produces the billions of punch cards Hitler needed to continue his war and the total annihilation of Jews. This book shows in detail the carefully constructed covert alliance between IBM and the Third Reich, and how IBM founder and president Thomas Watson cooperated with the Nazis. It's not an easy book to read, but an astonishing report on how a globalized company ignored moral ethics, laws and borders for the sake of profit. Above all, this book answers the most important question: how did Hitler get the names of all these Jews? IBM and the Holocaust The
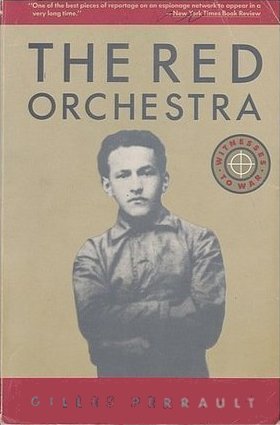
Red Orchestra - Gilles Perrault
Trepper however seems to be a ghost,
getting away each time, while the ring around his
organization is closing slowly. It's a detailed document
on how Soviet spies operated in Europe, and the battle
between Wehrmacht and Gestapo SIGINT units and the
different Soviet cells, broadcasting German secrets to
Russia.
|