What is Cryptography?
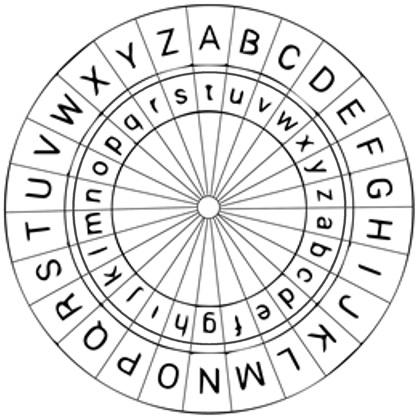
The readable information is called plaintext or plain data. The process of making that information unreadable is called encryption or enciphering, performed by a crypto algorithm, also called cipher. The encryption algorithm is a series of mathematical, technical or text-manipulation steps. Such algorithms are often a combination of substitution (replacing), fractioning (splitting) and transposition (moving). The crypto algorithm is controlled by a secret key, sometimes called password or passphrase. The result of encryption is a ciphertext or cryptogram. On crypto machines, the key is determined by the settings on the machine. The key is known only to those who are authorized to read the information. The process of retrieving the original information is called decryption or deciphering. Retrieving the original plaintext or data should be impossible without having the proper key or take so long that the information has become obsolete and useless. Cryptanalysis is the study and analysis of existing encryption algorithms or ciphers, to assess their quality and to find weaknesses and methods to reverse the encryption process without having the key. Cryptanalysis is essential to ensure that newly developed crypto systems are secure, and to determine the proper rules and measures to correctly perform encryption. Cryptography (making) and cryptanalysis (breaking) are two branches of the field of cryptology. Decryption without the proper key is a cryptanalytic attack, also referred to as breaking or cracking a cipher. A cryptanalytic attack can exploit weaknesses in the crypto algorithm, the key used, the crypto device, or errors in implementing essential procedures. There are various methods to attack a cipher. Some are standard techniques, and others are tailor-made for one particular message or a specific algorithm. A ciphertext-only attack is when the cryptanalyst only has access to the ciphertext. The known-plaintext attack is when the cryptanalyst has access to both the ciphertext and a corresponding plaintext, parts of the plaintext, or an assumed plaintext, which can assist in retrieving the corresponding key and in turn decrypt other messages with that same key. Another way to find the proper key is to try out all possible keys, the so-called brute-force attack. This technique is only useful when the message can be deciphered before the usefulness of the information in the message, i.e. tactical value, is expired. Multiple messages, encrypted with the same key, could also pose a risk. Such messages are called "in depth" and could help to determine the algorithm used, or the key applied. The more "in depth" messages are available to the codebreaker, the more chance there is to find patterns that help to decrypt the message. To limit the number of "in depth" messages that are encrypted with the same key, the users are often divided into many smaller groups, units or geographical locations, each with their own set of unique keys. This will limit the number of "in depth" messages, and the compromise of one key will not affect all users. This system is called compartmentalization. Codes are another technique to prevent information from being read. Codes don't use a cryptographic algorithm but codebooks, code sheets or code words to encode (i.e. convert) plaintext into unreadable information, or to compress (i.e. shorten) to save characters, or a combination of both. The resulting code could be a combination of letters, numbers, or a word. Depending on the codebook, AIRPLANE might be encoded into EBXLM, 582467, or GERONIMO. A famous code word was OVERLORD, the Allied invasion of Normandy. Both sender and receiver must always have a copy of the same code or codebook. Extensive use of the same codes will eventually reveal their true meaning, requiring additional encryption of the code (i.e. superencipherment) or a frequent change of alle codes, causing cumbersome logistics, especially with large user groups. Some codes convert characters into another form, such as binary ASCII code, Morse code, or the ITA2 teleprinter code. These are commonly known to the public and provide no security whatsoever. The expressions encode and decode are often incorrectly used to indicate encryption, and one should therefore always look at the context in which the expression is used. Ever since mankind has existed, people have had secrets, and other people have wanted to know these secrets. The earliest forms of cryptography were done with pencil and paper and obviously only available to people with a good education. There were two main types of classical ciphers. The substitution ciphers in which letters, words or sentences are replaced by other letters, words or symbols, and the transposition ciphers in which the letters in a message are rearranged. The earliest mentioned transposition cipher was the scytale, where a leather strip is wrapped around a wooden stick with a certain diameter. The text is written along the stick in, say, four rows. The leather strip is removed from the stick, and the original text can only be read by wrapping the leather strip around a wooden stick with identical diameter. One of the earliest substitution ciphers was the Caesar cipher or Caesar shift, in which the letters of the alphabet are replaced by the letters of a second alphabet that is shifted a fixed number of positions against the normal alphabet. It was named after Julius Caesar who used it to communicate with his generals during his military campaigns. This cipher evolved in the 15th century into Alberti's cipher disk and later the Vigenére cipher with multiple shifts (see cipher disk at the top). Cryptography was used to protect secret communications from military leaders, diplomats, spies, and religious groups. Unfortunately, most early ciphers revealed statistical information that could be used to solve them. As early as the 9th century, Arab mathematicians discovered frequency analysis and developed methods to solve those ciphers. This was the beginning of the race between codemakers and codebreakers. Frequency analysis proved to solve many ciphers, and it was not until the invention of the polyalphabetic cipher by Leon Battista Alberti in the 15th century that codemakers were one step ahead of the codebreakers. Polyalphabetic ciphers such as Vigenère use several sets of alphabets during the encryption process. For centuries, these ciphers were considered unbreakable, until Charles Babbage developed the techniques of multiple frequency analysis in the 19th century. Cryptography was used extensively by governments to protect their diplomatic mail. In the 18th century, all major European countries began to employ cryptologists to protect their communications, primarily sent through the postal service, or to break the encrypted messages from other countries. These agencies became known as Black Chambers. Some of the most notorious Black Chambers were the Austrian Geheime Kabinets-Kanzlei in Vienna, the French Cabinet Noir, and later the British Room 40, notorious for their great skill in intercepting and decoding all kinds of military and diplomatic mail. Cryptography soon became an important weapon in politics and in the many wars in Europe. Towards the end of the 19th century, important steps were taken in the development of cryptography. Auguste Kerckhoffs was one of the most important men who changed cryptography from an obscure art to a science, based on mathematics. It was Kerckhoffs who formulated the fundamental principle that encryption should never depend on the secrecy of the system, which would sooner or later be known, but should depend solely on the secrecy of the key. Many new manual pencil-and-paper ciphers, also called hand ciphers or manual ciphers, were developed and used during World War I, with varying degrees of success. These included the ADFGVX, Playfair, and Double Transposition. All were based on transposition, substitution, and fractionation of letters. An important invention was the one-time tape encryption for Telex (i.e. teletypewriters) by Gilbert Vernam in 1917. He realized that when a Telex signal was mixed with a truly random key, as long as the length of the message, the message would be unbreakable. Pencil-and-paper versions of his invention soon followed. With the advent of wireless communications, the need for secure communications for both military and civilian use grew exponentially. The cumbersome and time-consuming hand ciphers could not keep up with the growing demand, and this led to the development of all kinds of cipher machines. In 1913, George Fabyan founded a private research laboratory in Geneva, Illinois, which pioneered modern cryptography, later known as Riverbank's Department of Codes and Ciphers. During World War I, Riverbank assisted various U.S. government departments with cryptanalysis and trained military personnel. Their most famous codebreakers were Elizebeth Smith and the renowned William F. Friedman, who later married. After World War I, two types of machines dominated the market. The electromechanical rotor machines such as the German Enigma and Siemens & Halske T-52, the British Typex, and the fully mechanical pin-and-lug machines such as the Hagelin series. Although machines took over much of the work, manual pen-and-paper ciphers remained in us for short-time tactical purposes where the time to cryptanalyze them would render the tactical information useless. The secure Double Transposition manual cipher was used until the end of World War II, by both the Allied and Axis powers. The German Army introduced the Rasterschlussel 44 in 1944 and it took the Allies too long to crack the code for tactical use. The one-time pad was used during World War II and throughout the Cold War for covert operations by intelligence agencies. The system is still in use today and remains unbreakable, regardless of any future technology, if properly implemented. From 1923 on, Elizebeth Friedman worked for the U.S. Navy and the Treasury Department, breaking encrypted communications of rum runners during the Prohibition, drug runners, smugglers, and domestic and international criminal activities. William Friedman wrote eight monographs, of which "The Index of Coincidence and its Applications in Cryptography" was the most important of modern cryptography at the time and remains relevant today. All major countries realized the importance of intelligence gathering and new organizations saw the light. During the Second World War, Room 40 in Britain was reorganized into the Government Communications & Cipher School (GC&CS), which played a decisive role during the Second World War. Amongst their most famous cryptologists were Alan Turing, Alastair Denniston, Dilly Knox and John Tiltman. GC&CS was the wartime predecessor of current British Government Communications Headquarters (GCHQ). In the United States, the Signal Intelligence Service (SIS) and the Communications Security section of the Office of Naval communications (OP-20-G) were the most important code breaking organizations with legendary cryptologists such as William Friedman and Meredith Gardner. Elizebeth Smith worked for Coast Guard Cryptanalytic Unit 387 and the FBI, leading the breaking of the Enigma machines, used by German spies in South America during the Second World War. The Second World War led to improved cipher machines like the American SIGABA and SIGCUM, and the German Lorenz SZ-40 and Schlusselgeraet 41. To break the huge amount of encrypted message traffic the codebreaker had to build new, automated machines, which lead directly to the development of the first digital computers. In Bletchley Park, Max Newton and Tommy Flowers developed the Colossus, a digital programmable computer to break the Lorenz SZ-40/42 messages. This was the first step in the evolution of cryptography towards the new computer age. However, new improved electro-mechanical cipher machines such as the TSEC/KL-7, Fialka M-127 and Hagelin CX-52 were designed and remained in service until the 1980s, when digitalization really broke through. It was Claude Elwood Shannon who laid the foundations for modern cryptography in 1948 with his famous Information Theory. William Friedman became head of the crypto division of the U.S. Armed Forces Security Agency (AFSA) in 1949 and chief cryptologist for its successor the National Security Agency (NSA) in 1952. Elizebeth and William Friedman had led the United States into to modern age of cryptography. The development of electronics and digital computers after the Second World War made it possible to create encryption algorithms, far more complex than before. The new computer algorithms were no longer based on simple substitution, transposition and fractioning of letters and words, but on a large number of complex operations on data bits. One of the first block ciphers - encryption performed on blocks of data bits - was the Lucifer cipher, designed by Feistel and Coppersmith for IBM, and based on what is known as a Feistel network. Lucifer was the precursor to Data Encryption Standard (DES), the very first cryptographic standard. However, the computer revolution not only led to better encryption systems, but also to faster and better codebreaking techniques. The race between codemakers and codebreakers continued unabated. Absolute security was one of the reasons that one-time pad systems remained in use for Telex traffic and the like until the 1980s, although the expensive and complex key distribution, a typical disadvantage of one-time pad, made it affordable only to the military and diplomatic services. Until the 1970s, the crypto community remained very closed and was mainly controlled by government agencies. The public release of DES and the RSA public-key algorithm were a turning point in the spread of cryptography. Following Kerckhoffs' principle, newly designed crypto algorithms were made public so that they could be subjected to extensive academic research. The advantage was obvious. A large open crypto community could evaluate new algorithms, discover weaknesses and suggest improvements or reject the use of a weak algorithm. This led to a 'survival of the fittest' situation, which resulted in quality encryption standards. Some of the most widely used and publicly available symmetric algorithms today are the Advanced Encryptions Standard (AES) and the International Data Encryption Algorithm (IDEA). However, secret algorithms are still being developed and used, mainly by government agencies. Another type of computer algorithms are stream ciphers. They were developed in response to the key distribution problem for long keys, as used in systems such as one-time pad. While a block cipher performs a cryptographic function on a fixed number of plain bits, a stream cipher produces a continuous stream of pseudo-random values, mixed with the plaintext bits. Pseudo-random, because stream ciphers are deterministic and never produce true randomness, required for one-time pad encryption. Some well-known stream ciphers are RC4, SEAL, SOBER, and FISH, The most important development for modern cryptography was public-key cryptography. Until 1970, all encryption was based on symmetric key algorithms. Both encryption and decryption are performed with the same key and both sender and receiver of an encrypted message must use the same key. The disadvantage of this system is a complex key distribution system with several security problems. The invention of the asymmetric key algorithm by James Ellis was a revolution in the world of cryptography. In asymmetric key cryptography, two keys are used. A public key for encryption, and a secret private key for decryption. The public key cannot be used to decrypt the information. This solved the expensive and risky problem of secret key distribution. From now on, you could make your public key available to everyone. With that public key, anyone can encrypt a message intended for you, but only you, with your private secret key, can decrypt the message. No longer a need to share a secret key! James Ellis' invention at the Government Communications Headquarters (GCHQ), the successor to the GC&CS, remained top secret. However, Whitfield Diffie and Martin Hellman proposed an asymmetric key algorithm in 1976, and Ronald Rivest, Adi Shamir, and Len Adleman invented RSA, another public key system, in 1978. Because of their solution to the secret key distribution problem, the Diffie-Hellman and RSA algorithms are among the most widely used crypto algorithms in the world. Public key algorithms are based on the computational complexity problem. The Diffie-Hellman algorithm is based on the discrete logarithm problem, and RSA is based on the factorization problem of large prime numbers. Asymmetric key algorithms require large keys and heavy computations, making them suitable only for encrypting small amounts of data. Therefore, the message or data is encrypted with a strong traditional symmetric algorithm under the control of a secret key, and that secret key is then encrypted with an asymmetric key algorithm to securely exchange the secret key. All this in one convenient automated package. Today, this principle is used countless times a day, without anyone knowing, by anyone visiting a secure website with https. Another popular implementation is Philip Zimmermann's PGP, a combination of a strong symmetric block cipher, practical asymmetric public key cryptography, and a digital signature, to securely send emails or sign documents. Authentication, data integrity, and digital signatures are another important area of cryptography. We can protect passwords on a server and trust the contents of any data file, using a hash function, a special one-way function that uses a crypto algorithm to take an input of any variable length, such as a password or computer file, and return a unique fixed-size hexadecimal string, called hash value. This unique hash cannot be used to calculate and retrieve the original password or file, hence the name one-way function. It is therefore impossible to obtain a password from the hash value or to manipulate a document without changing the accompanied hash value. Even changing a single bit will result in a completely different hash. Any website that takes security seriously will only store the hash value of your password on their server. When you login to your account, your password is first converted into the hash value, compared to your original hash on the server, and only accepted if both hashes are identical. Even if an attacker obtains the hash on the server, it will be impossible for him to use that hash to calculate the original password, required for the verification process. The authenticity of a received or downloaded document, software, or other type of digital file can be verified by calculating its hash value and comparing it to the hash value published by the original author of the file. Hash calculators are available for free online, or as standalone software. SHA256 and SHA512 are popular hash algorithms, and the SHA-3 series, ranging from SHA3-224 to SHA3-512, are some of the most secure hash algorithms. Note: You should never use an online hash calculator tool for active passwords, as your password may not remain private! This process can also be fully automated with a digital signature, using a public-key algorithm. When an author signs his document or file, a unique hash value of that document is calculated and encrypted with the author's private key. The result is a digital signature. The recipient of a document decrypts the signature with the original author's public key and checks the hash value to confirm the authenticity of the document. Signature integrity requires a Public Key Infrastructure or PKI, where a trusted Certificate Authority (CA) generates and stores the required secure keys and issues digital certificates. Is cryptography important to you? Absolutely! Today, cryptography is integrated into every aspect of your life to protect all your communications. When you surf the Internet, send emails, or log into your favorite social network, that connection is secured by HTTPS, the Hypertext Transfer Protocol Secure. HTTPS uses strong cryptography to prevent eavesdropping, tampering, and forgery of messages. And it’s not just your PC that uses encryption. When you shop, your customer cards are scanned, and cryptography protects your personal information. When you use your credit card to pay or withdraw money from an ATM, the transaction is processed securely by your bank. The information on the chip of your ID card or health insurance card is encrypted. When you call someone on your mobile phone, your digitized voice is encrypted to prevent eavesdropping. The remote control for your car’s central locking system communicates with your car to generate unique keys, protected by cryptography. Imagine our digital world today, without cryptography. Your life insurance broker could simply use the Internet to read your medical files. Anyone could check your criminal record without permission. What if your employer could read what you do with your money? Cryptography prevents people from illegally invading your privacy. The most important advantage of cryptography is indeed privacy. Today, our lives are completely digitized. Almost all of your private information is stored in one of the many databases of the government, police, city services, banks, commercial firms, health care services, and so on. All of this information can be exposed to unauthorized people. We must maintain control over the technology that ensures our privacy. Cryptography protects the right to privacy and the right to communicate confidentially. Secure communications can protect one’s intimate private life, business relationships, and social or political activities. These basic rights are enshrined in the constitution of many, but not all, countries. Of course, it is illegal to use cryptography for criminal purposes or to plan terrorist acts. However, this does not mean that the use of cryptography should be illegal. Just because guns, knives, or crowbars can be used for illegal purposes, that doesn’t mean they should be considered illegal. In fact, it’s pointless to make cryptography illegal, because criminals simply don’t care about the law. If you ban cryptography, then only criminals have cryptography and privacy. But even the most liberal and democratic countries have laws that control the use of cryptography, and some countries have stricter laws than others. Some governments don’t allow their citizens to use cryptography because it limits their ability to monitor them. Laws are often a trade-off between protecting the privacy of the individual and the security of a country or the fight against crime. Democratic countries typically allow cryptography for personal use and have legal mechanisms to circumvent the right to privacy with a court order in the event of a criminal investigation or a threat to the nation. The boundaries between legitimate surveillance and state-organized invasion of privacy are often debated, even in democratic countries. Depending on the country, laws on cryptography may partially restrict certain types of cryptography, only allow government-licensed systems, limit the strength of the encryption, or require key retention. Some laws may compel someone to hand over his decryption keys, upon a court order. There are laws that restrict the import or export of cryptographic software, equipment and knowledge, or even treat the export of cryptography as weapons export. You may not object to your current government having the ability to invade your privacy “if they really need to”, and only if the Department of Justice approves, but governments change, and what you consider a democracy today may be a totalitarian state tomorrow. That’s why we should be able to use strong encryption without restrictions to protect our basic rights, today and tomorrow. Is cryptography important to you? You bet it is! More about Cryptology on this
Website
More on Cryptography (off-site
- opens in new tab)
|
 Cryptography, from the Greek krypto (hide) and
graphein (write), is the study and implementation of
techniques to hide or protect information from being
read. The information can be written text, electronic
signals such as Morse code, teleprinters, audio, or
digital information such as computer files, e-mails,
sensitive government or commercial networks, banking
software, and all kinds of data transmissions and
technical signals.
Cryptography, from the Greek krypto (hide) and
graphein (write), is the study and implementation of
techniques to hide or protect information from being
read. The information can be written text, electronic
signals such as Morse code, teleprinters, audio, or
digital information such as computer files, e-mails,
sensitive government or commercial networks, banking
software, and all kinds of data transmissions and
technical signals.