Electronic communications should not
only be efficient and reliable, but also secure. This
means that it should be impossible for the adversary to
intercept and read sensitive information. The most
obvious solution is encryption, making the message
unintelligible for anyone who eavesdrops on insecure
communications channels. Cryptography has been used
extensively since the early 20th century to protect the
rapidly expanding military communications. However, in
the 1940s it was discovered that, despite using secure
encryption algorithms, the crypto equipment itself could
unintentionally emanate signals that enable the adversary
to read the communications. The answer to this threat was
TEMPEST. The codename TEMPEST is not an acronym,
but it is sometimes written out as Telecommunications
Electronics Material Protected from Emanating Spurious
Transmissions. This refers to the whole of technical
recourses, standards and regulations to protect
communications equipment against unwanted radiation of
signals that might be intercepted, analyzed and exploited
by the adversary. From Small Signal to Big
Problem During the
Second World War, the U.S. Signal Corps encrypted
high-level teletype communications with one-time tapes
(OTT's). This system uses Vernam’s original
principle where a five-bit teletype signal is mixed with
a key tape, containing random five-bit values. The system
is quite simple but absolutely unbreakable, even with
todays or any future technology. A famous example is the
Washington-Moscow hotline.
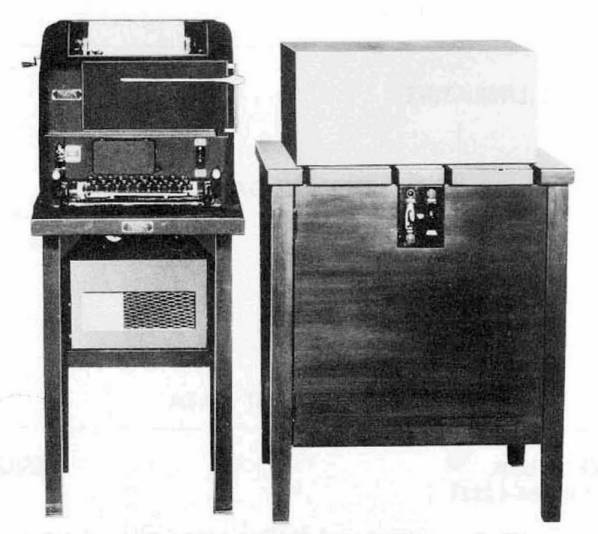
Bell Telephone provided the Signal Corps with the 131-B2 PYTHON mixer that combined the teleprinter output signal with the one-time tapes. The machine was also known as the as AN/FGQ-1 or CSP-2599 in military nomenclature. In 1943, Bell engineers discovered little spikes on the screen of an oscilloscope near a working one-time tape mixer. Upon further investigation, they discovered that the oscilloscope had picked up electrical signals, emitted by the one-time tape mixer. To their surprise, the spikes on the screen represented the readable unencrypted five-bit signal. They could read the plain text directly from their oscilloscope! It was obvious that these undesirable interference signals arose from the crypto equipment, even before the signal was encrypted. Bell Labs informed the Signal Corps about this dangerous vulnerability in their crypto system. The Signal Corps, however, met Bell’s findings with a lot of skepticism and believed that it would be impossible for an adversary to intercept these tiny electrical spikes in operational conditions. They answered that, and I quote, “we can’t bring our cryptographic equipment to a screeching halt based on a dubious and esoteric laboratory phenomenon. If this is really dangerous, prove it." Bell Labs was assigned a building at Varick Street, New York, right across the Signal Corps crypto center. During an improvised test they recorded signals over a one-hour period. Within three hours, the engineers succeeded in recovering 75 percent of the plain text of so-called encrypted traffic, and this without any physical connection to the crypto center. Shocked by the results, the Signals Corps asked Bell to examine the problem and to modify the 131-B2 mixer. After six months, Bell Labs had identified three phenomena. The first problem were small radio emissions of electrical pulses, carrying at least half a mile, caused by electrical contacts in relays. The second issue was induction. Some of the emitted pulses were picked up by the communication lines and travelled more than a mile on those lines. The third phenomenon was the radiation of magnetic fields, originating from coils in relays, reaching some 30 feet but virtually impossible to suppress. To make it even worse, all the different types of radiation occurred on a very wide frequency spectrum. The solutions to suppress these unwanted signals were shielding to contain the emitted signals, filtering to block induction on lines and masking the remaining signals by adding interference signals. The latter of course proved unacceptable for the Radio Advisory Committee. The modified 131-A1 mixer was fitted with various filters and completely encapsulated, causing heat dissipation problems. The machine was very heavy and difficult to operate and maintain. The Signal Corps turned down the impractical monster and opted for the only other solution: they ordered communications centers to be located within a controlled free zone of at least 100 feet. Case closed. Seven years later the problem was long forgotten when it was rediscovered in 1951 by the CIA during tests with the very same 131-B2 mixer. They were able to intercept plain text half a mile along a communications line. The CIA asked the American Forces Security Agency (AFSA) if they were interested in this problem. Of course, they were. AFSA solved the induction problem, but some emissions remained. This resulted in the first AFSA radiation policies, providing recommendations about how to securely operate crypto devices. With too small a budget, NSA took over the research to eliminate the annoying signals from its precursor AFSA. More problems surfaced. Acoustic radiation of crypto devices provided information that could be exploited and electrical motors and coils in crypto machines and teleprinters caused voltage variations on the electrical net, revealing additional intelligible information. By then, five problems were identified, and emission distances kept increasing. This initiated a race between the engineers who searched for solutions to contain the problem and the analysts who found new ingenious ways to intercept the persistent signals at even larger distances. They were criticized for finding methods to increase the distance and were asked to focus on decreasing the distance. Unfortunately, another even more serious problem surfaced. Crypto equipment, connected to radio transmitters, emitted very weak plain text signals. These signals were picked up by the nearby transmitter and modulated onto the transmitted radio waves. The plain text piggy-backed on the transmitter’s powerful radio waves, making it possible to filter out and read the plain text at distances of tens or hundreds of miles. This was by far the most serious security issue. In 1956, after years of research and numerous unsuccessful experiments, the Navy Research Laboratory came up with the first major breakthrough. Instead of trying to filter and shield the annoying signals, they simply reduced the cause of the problem. By running the critical components on a much lower voltage and replacing electromechanical components by transistors and other semi-conductors, they reduced the amplitude of the signal considerably or eliminated it completely. A signal with an amplitude of 2 volts simply doesn’t carry as far as a 120 volts signal, and switching currents with transistors avoided the sparking of relay contacts. NSA took over the technique of filtering and lower voltages for all new one-time tape mixers. The emission distances were reduced from half a mile to a mere 20 feet. All new equipment, from crypto machines to teleprinters and other on-line devices were now developed with the gained knowledge. The first extensive regulations on TEMPEST were drafted by the Military Communications Board (MCB) in 1958. The classification of the various problems and recommendations were finally put on paper and generally accepted. Canada and the U.K. followed in 1959 and the first real Communications Security or COMSEC plan was written out the same year. The consequences of the COMSEC policies were far-reaching. Many insecure devices, buildings and procedures were identified, and security measures were taken. Technical test and standards for communications equipment followed. The policies regarding TEMPEST and COMSEC were finally implemented in 1966 and a TEMPEST laboratory for non-crypto equipment was founded in 1970. On the right you see a fine example of mid 1960’s TEMPEST design. The KW-7, a second-generation teletype encryption unit, was fully filtered, shielded and operated on low voltage electronics. In front of the machine, on the left, is one of its 12 cards, carrying 21 small modules. Each module contained several transistors, diodes and passive components. These "Flyball" modules were the precursor of todays integrated circuits or IC’s. The KW-7 was quite an improvement over the electro-mechanical 131-B2 in its wooden cabinet. These technical improvements and regulations came none too soon. Already in the early 1950s, the Soviets published a comprehensive set of regulations on suppressing signals from teleprinters and communications equipment. These regulations were much stricter than generally accepted in their industry. The Soviets clearly recognized the potential hazards of those annoying signals and were rightly worried. Undoubtedly, they also understood the potential of intercepting these signals from early on. Whether they also exploited the ignorance of their adversaries remains hidden in the Soviet intelligence archives. Today, many security related communications devices are TEMPEST designed. Probably the largest TEMPEST object on earth is the massive NSA building at Fort Meade, encased in copper meshing to shield it from eavesdropping. TEMPEST now resorts under the broader EMSEC (Emission Security). Today’s electronics provide new possibilities to suppress unwanted radiation but also enable the development of new sophisticated and very sensitive equipment to intercept those signals. The development and operation of secure communications equipment will always remain a technical challenge.
External Links and References
(open in new tab)
|