About Operation Tinker Bell and the Cryptologic Challenge You will experience real spy tradecraft
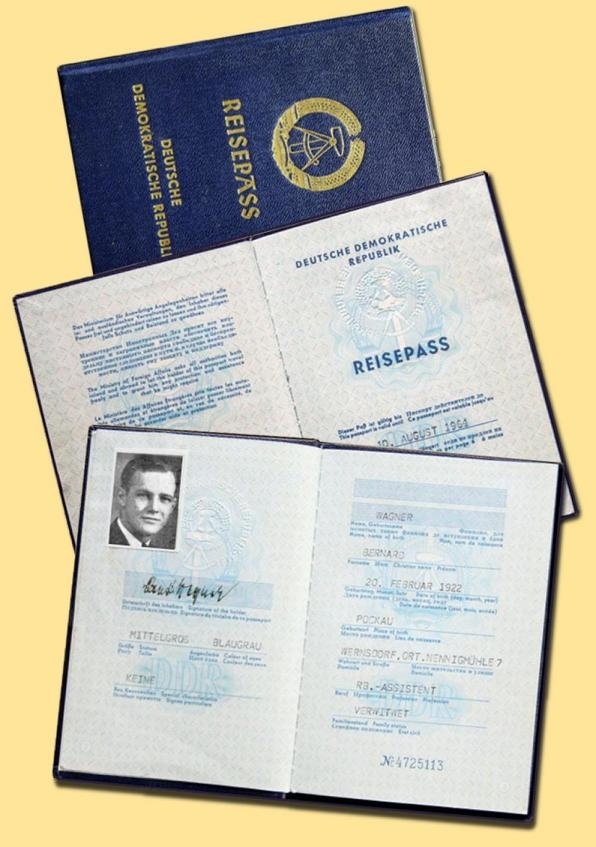
first-hand, including illegal border crossings, fake
passports, safe houses, the dreaded East-German Stasi and
Czech StB secret police. Clandestine meetings are
supported by British intelligence, CIA transmitter sites
in West Germany, and the U.S. Army Security Agency
provides SIGINT support. The Cold War at its height, with
authentic details, many historical photos, as real as it
gets. Join the operation, complete the
mission, and get your name on the Wall of Honor! Historical Context The 1961 U.S. invasion of Cuba ended in
disaster, the 1962 Cuban missile crisis almost caused
nuclear war, and John F. Kennedy was killed in 1963. It's
1964 and the Cold War is raging. U.S. secretary of
defense McNamara increases military aid to South Vietnam
and President Johnson prepares to enter the Vietnam
conflict. There is still no peace in Korea and the Iron
Curtain split Europe in half. Increasingly more East
Germans flee to the West, and political tension grows in
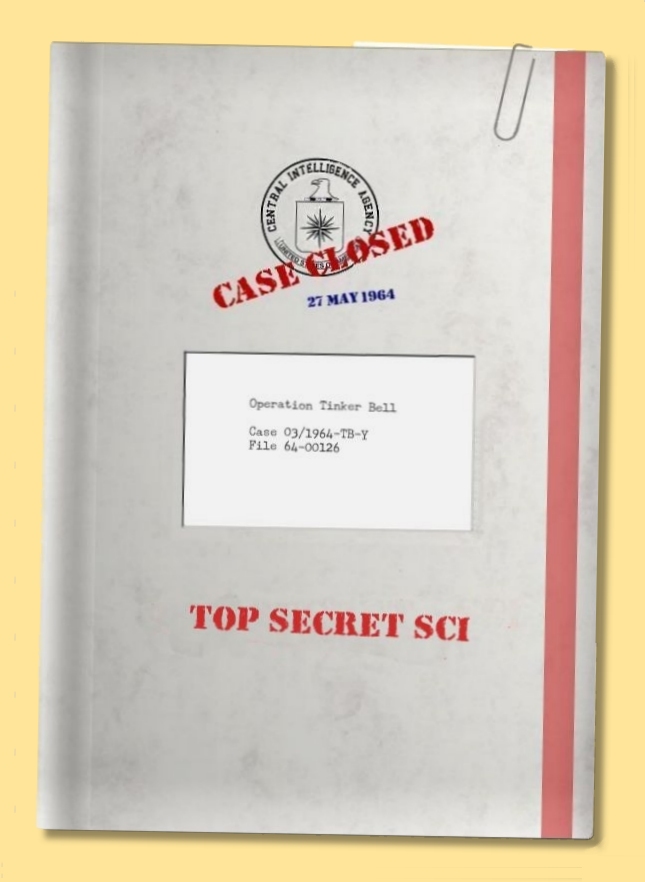
Czechoslovakia. The Operation The CIA Science & Technology
Directorate and the National Security Agency are most
interested. Novak is assigned to Rogozin as his case
officer and CIA headquarters in Langley designates the
codename GYMNAST to the defector. Novak persuades Rogozin
to return to Moscow, assume his normal duties and collect
additional intelligence before defecting in the near
future. Rogozin’s contact person in Moscow is Roman
Danilov, a CIA operative under the cover of UP
journalist, attached to the U.S. embassy to Moscow. The
first meeting between Danilov and Rogozin is scheduled
for April 5. On the day of the meeting, Danilov
leaves his apartment at Povarskaya street 29 at 11:35
hours Moscow time. The next morning at 08:15 local time
(00:15 in Langley) CIA station Moscow contacts its
headquarters in Langley. Danilov failed to report after
his meeting with Rogozin and is nowhere to be found. The subsequent investigation confirms
that Roman Danilov disappeared without a trace. There's
no word of KGB Colonel Rogozin and the defector turns out
to be dangle, a bait to identify CIA agents, or a KGB
staged recruitment that went horrible wrong. That same
morning, Danilov is officially reported missing. Bill
Hensley, head of CIA’s Soviet Division, is furious
about the loss of his operative and Robert Novak is
ordered to track down Rogozin by any means available.
Operation Tinker Bell, the search for the fake KGB
defector, has begun. Your Task Start by visiting the COMCEN, the CIA's inner sanctum, to update your
knowledge of how Langley and its stations abroad
communicate with each other by cable, and with agents in
the field by clandestine radio transmissions. You will
learn to use the 1960s state-of-the-art TSEC/KL-7 cipher
machine for secure communications between CIA stations
and embassies, and one-time pad encrypted messages, sent
by numbers stations or by operatives in hostile
environments. To understand the tools and environment
in which you will be operating, catch up reading about
the TSEC/KL-7, numbers stations, one-time pads and Cold War signals. Our
blog covers Signals Intelligence
Keep a
detailed record of all decrypted messages to submit your
work later on. To gain a better understanding of the
operation, we advise you to carefully examine all
information such as places, services, unit, and names
that you find in the messages. Also check the red info
buttons Submit Your Messages Once finished, send an e-mail with your name and country, and attach all
decrypts in one .txt file (UTF-8 format in Notepad or
TextEdit). If you successfully complete the operation,
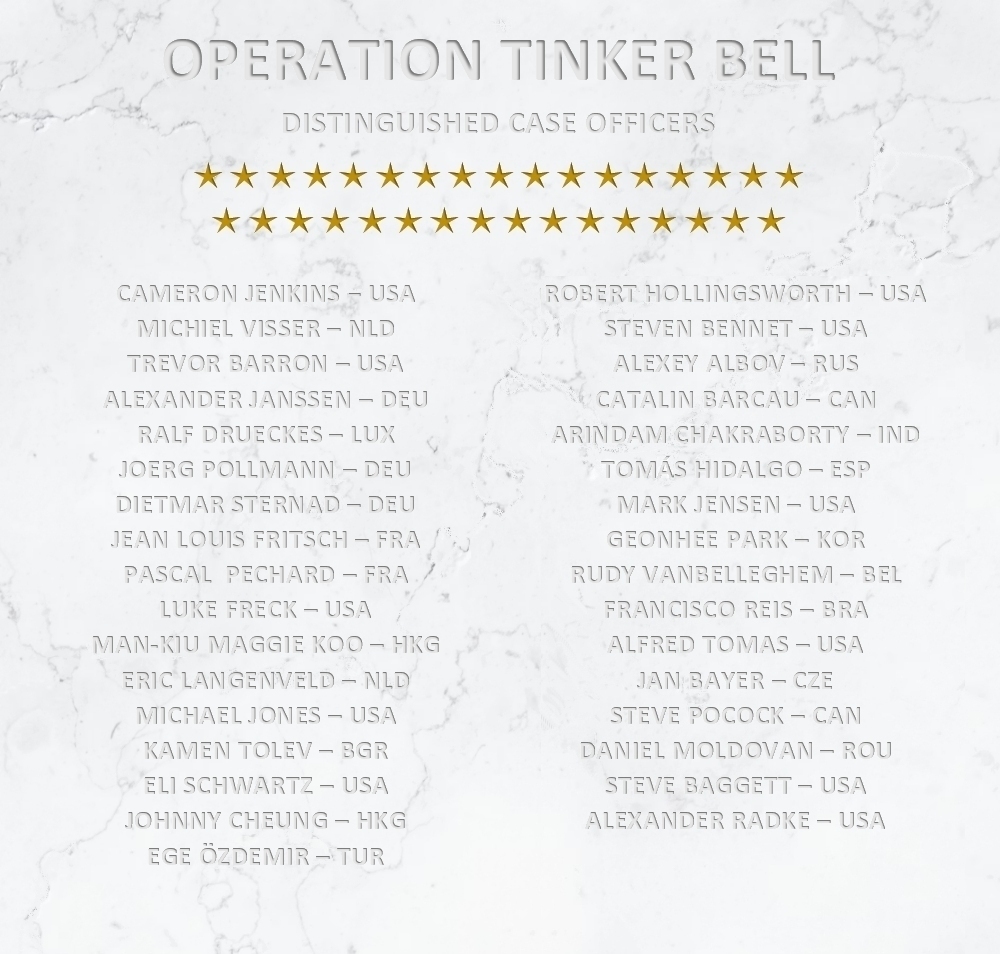
your name will be engraved in the Wall of Honor. It is
not allowed to publish any plaintext solutions. If you
have questions or comments, feel free to contact us. The Wall of Honor was only established in
2020, and those who completed the mission earlier can
contact us.
Cipher
Machines and Cryptology |
 March
17, 1964. KGB Colonel Alexander Rogozin contacts the U.S.
Embassy to Turkey and CIA officer Robert Novak from the
Soviet and Eastern Europe Division is sent to Ankara to
meet Rogozin. Novak’s assessment is that Rogozin is
disillusioned in the Soviet political system, his
military career, and his marriage. He wants to defect to
the United States and his knowledge of communications
technology and cryptology could be valuable to U.S.
intelligence.
March
17, 1964. KGB Colonel Alexander Rogozin contacts the U.S.
Embassy to Turkey and CIA officer Robert Novak from the
Soviet and Eastern Europe Division is sent to Ankara to
meet Rogozin. Novak’s assessment is that Rogozin is
disillusioned in the Soviet political system, his
military career, and his marriage. He wants to defect to
the United States and his knowledge of communications
technology and cryptology could be valuable to U.S.
intelligence.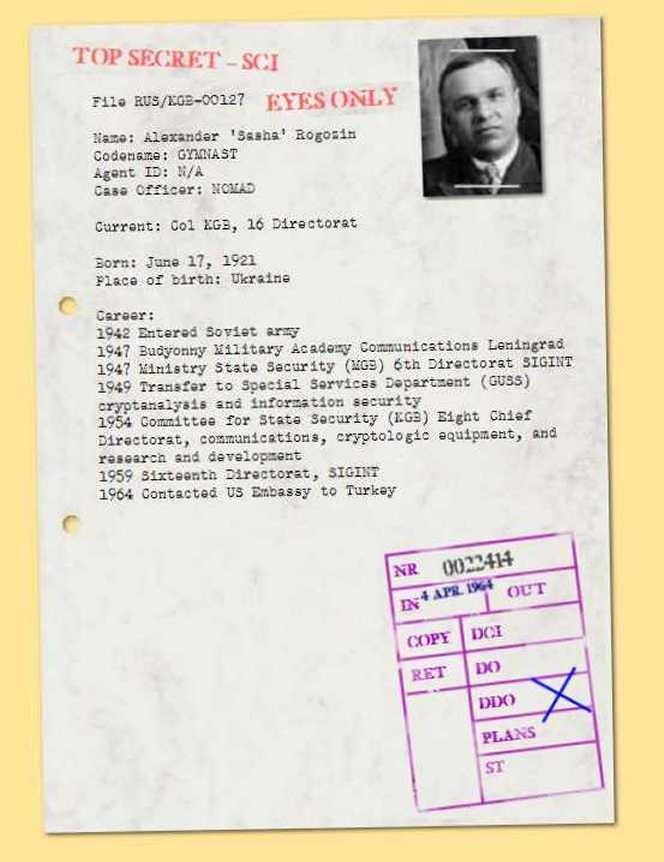 Next,
examine all
Next,
examine all