| 1917 |
|

M-94 |
The M-94 (CSP-448) is a
cryptographic device, similar to Thomas
Jefferson's wheel cypher or Bazeries' cylinder.
The M-94 was developed in 1917 by U.S. Major
Joseph Mauborgne and in 1921 introduced in the
U.S. Army. The M-94 consists of 25 aluminium
discs, arranged as a cylinder on an axle. Each
letter disc has a scrambled alphabet. A message
is encrypted by turning each disc until all
plaintext is arranged on one line. A random
chosen other line on the M-94 is then read off as
ciphertext. The secret key of the system was the
agreed upon order of the discs on the axle of the
M-94. Although the M-94 provided a low-level of
security, it still required extensive
cryptanalysis to break, and was good enough for
tactical purposes. The M-94 remained in service
until 1943. [1] [2] [3] |
| 1918 |
|

Hebern |
The Hebern rotor
machine, invented by Edward Hugh Hebern, was the
first rotor cipher machine, with one single
rotor, containing scrambled wiring. When a key is
depressed, the electrical current travels through
the scrambled wiring and either print a letter on
an electrical typewriter or a light bulb. The
scrambled wiring has the effect of a substitution
cipher, and the most important difference with
the simple substitution is that the rotor turns
on each depressing of a key. Although the machine
never became a commercial success, due to the
limited cryptographic strength, it did lay the
foundations for many future more advanced rotor
cipher machines. [1] [2] [3] |
| 1920 |
|

Kryha |
The German Kryha is a
fully mechanical cipher machine, developed by
Alexander von Kryha and used from the 1920s until
the 1950s. The Kryha contains two concentric
alphabet discs, of which the inner disc steps a
variable number of places. The plaintext letter
is read from the outer disk and the ciphertext
letter from the corresponding inner ring. After
each letter, a lever is pressed to move to change
the position of the two rings, relative to each
other. A smaller version, called Lilliput, and a
large electrical version existed. The Kryha was
used by the German Diplomatic Corps and Marconi
England. [1] [2] [3] [4] |
| 1921 |
|

A-21 |
Arvid Damm developed
the A-21, which was commercialized by A.B.
Cryptograph, the predecessor of Hagelin Cryptos.
The machine uses a revolving drum with 26
alphabet strips that can be attached in any
order. The 26 combined alphabets are a scrambled
vigenére square with alphabets in reversed
order. For each encrypted letter, the drum steps
one alphabet strip further. A normal reference
alphabet is mounted in front of the drum and a
chain with low and high links controls the
position of the reference alphabet above one of
the two visible scrambled alphabet strips on the
drum.[1] |
| 1924 |
|

Schreibende Enigma |
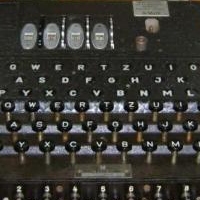
Already in 1918, the
German engineer Arthur Scherbius applied for a
patent on a machine he called Enigma. In 1924, he
developed the Handelsmaschine (Commercial
Machine), the first commercial Enigma machine,
using a principle similar to Hebern machine, but
with four stepping cipher rotors. The heavy
Handelsmaschine printed the ciphertext onto paper
with a printing wheel. He also developed the
Schreibende Enigma, also with two rotors but
printing the text with normal type bars. In 1924,
Scherbius introduced the Enigma A. The machine
had two rotors, the so-called reflector and a
lamp panel with 26 letters that replaced the
bulky printer system. The Enigma B had the same
principle, but had two interchangeable rotors, a
rotatable reflector and its rotors stepped on
each keystroke. The Enigma B Mark II had three
rotors and a fixed reflector. This design led to
the compact Enigma C, the predecessor of the
Enigma D. [1] [2] |
| 1925 |
|

B-21 |
In 1925, Boris Hagelin
developed the B-21, his first cipher machine. It
used two rotors in a 5 by 5 grid system and pins
on the rotors to control the stepping. The unique
design of pinwheels would become popular in many
of Hagelin's successors. The B-211 was a further
development of the B-21 where the text was
printed, introduces in 1932. [1] [2] [3]Meanwhile, the German Marine adopted in
1925 the Enigma C and named it Enigma
Funkschlussel C.
|
| 1926 |
|

Enigma D |
The Enigma D was the
successor of the Enigma C. The machine was
commercialized in different versions and sold all
over the world. Switzerland bought the Enigma K,
also called Swiss-K. Italy bought the Enigma D,
as did Spain during the Spanish Civil War. Japan
the Enigma T or Tirpitz Enigma. All of them were
broken by several Intelligence Agencies. [1] [2] |
| 1927 |
|

Enigma I
|
In 1932, the
Wehrmacht revised the commercial Enigma D to
improve the security of the machine. They added
the plugboard at the front of the machine, which
provided an enormous number of possible
combinations. This version, called Enigma I,
became known as the Wehrmacht Enigma and was
introduced on a large scale in the Heer (Army).
The Luftwaffe (Air Force) followed in 1935. The
Wehrmacht Enigma came initially with three
rotors. From 1939 on they were equipped with five
rotors. The Enigma I was used throughout the
Second World War. [1] [2] |
| 1931 |
|

Enigma G |
The German Abwher
(Secret Service) started using the Enigma G
(Zahlwerk Enigma), a securer version with a
gearbox to drive the rotors. The Wehrmacht
adopted the Enigma D and revises it to Enigma I
in 1932. This version is the first to use the
plugboard which increases the key space
enormously. It is this version that would become
famous as the German wartime cipher machine,
however in 1932, the Polish Cipher Bureau broke
into the Enigma message traffic. Their knowledge
was turned over to British and French
cryptologists prior to the invasion of Poland. [1] [2] [3] |
| 1935 |
|

C-35 |
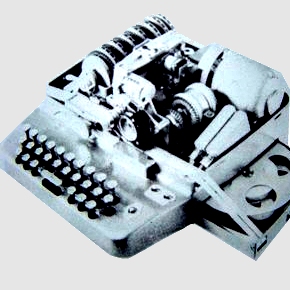
Boris Hagelin developed
the portable C35 on request of the French Cipher
Bureau. This was the first real pin-and-lug type
cipher machine. Five pinwheels, each with another
number of pins, controlled sliding bars on a
revolving drum. This drum is used as gearwheel
with a variable number of teeth, driving a
reciprocal alphabet. The machine output was
printed on a paper ribbon. [1] [2] [3] |
| 1936 |
|

T-52
|
The German Siemens
& HalskeT-52 Geheimschreiber, codenamed
STURGEON by the British codebreakers, was the
first important German high level teleprinter
cipher machine. The T-52 has 10 pinwheels that
step in a most complex way. The pinwheels control
the five-bit signals that is mixed (XOR) with the
five-bit teletype signal. [1] [2] [3] |

M-325
|
The M-325, codename
SIGFOY, was developed in 1936 by NSA cryptologist
William Friedman. The machine has four rotors and
a lamp panel with all letters of the alphabet.
Although developed for the U.S. Army, the M-325
was only used by the U.S. Foreign Services from
1944 until 1946, when it was discontinued due to
technical problems. [1] [2] |

C-36 |
The Hagelin C36 was
very similar to C-35 but had a protective casing
and another distribution of the lugs on the drum.
A later model had two movable lugs per drum bar. [1] [2] |
| 1937 |
|

TYPEX |
The British TYPEX was
an adapted version of the Enigma with several
important improvements. The increased security
and complexity meant that the message traffic of
this machine never was broken, unlike the German
Enigma. An estimated 12,000 Typex machines were
used in the UK, Canada, and New Zealand until the
1970's. [1] [2] |
| 1938 |
|

BC-543 |
The Hagelin C38 was a
variant of the Hagelin C-36. The Hagelin BC-543
was a variant of the C-38 that incorporated a
keyboard and both cipher and plaintext output. [1] [2] [3] |
| 1939 |
|

PURPLE
|
PURPLE (97-shiki O-bun
In-ji-ki) was a Japanese cipher machine, used by
their Diplomatic Services. Both British and US
cryptologists had already broken the PURPLE
message traffic before the attack on Pearl
Harbor. [1] [2] |

Lacida
|
The Polish Cipher
Bureau developed the Lacida, also called LCD. It
was a rotor cipher machine. Although similar to
the German Enigma it had some major security
flaws such as the lack of a plugboard, the
reflector design and the wiring. [1] [2] [3] Also in 1939, the German Kriegsmarine
(Navy) took over the Wehrmacht Enigma I and named
it the Enigma M3. They also extended the set of
rotors from five to eight.
|
| 1940 |
|

SIGABA
|
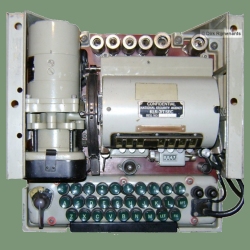
The ECM Mark II,
codename SIGABA, was the most important American
rotor cipher machine for high level
communications. The SIGABA had three banks of
five rotors each. The first bank were the main
rotors to encipher the alphabet. The second bank
of rotors scrambled four signals into one to six
signals. The third bank of rotors scrambled these
signals and used them to advance the main
encryption rotors in a complex pseudorandom
fashion. The SIGABA traffic has never been broken
and the machine remained in use until the 1950's.
[1] [2] [3] |

SZ-40 TUNNY
|
The
German Lorenz SZ-40, codenamed TUNNY by British
cryptologists, had 12 pinwheels and was similar
in design to the STURGEON. TUNNY was also used
for high level German communications. It was
broken by British cryptologists and they
developed the first electronic digital computer
ever, the top secret Colossus, to automate the
breaking of the TUNNY messages. The Colossus was
so secret that for many years the world believed
that the American ENIAC was the first digital
computer. [1] [2] [Colossus]
|

M-209
|
Hagelin succeeds in
selling the C-38 to the United States Armed
Forces. They produced a licensed version,
designated M-209, in large quantities as low
level tactical cipher machine. Approximately
140,000 M-209's were produced. [1] [2] [3] [4] [Simulator] |
| 1941 |
|

SG-41 |
Schlusselgerät 41 or
SG-41, developed by Fritz Menzer, was the last
German cipher machine, produced during WW2. Its
encryption principle was similar to the Hagelin
pin-and-lug machines, with some changes to
improve security, making it far more secure than
the Enigma machine. Production started in 1943,
and although crypto experts preferred to replace
the Enigma with the SG-41, tens of thousands of
Enigma machines were already in service. Later
on, shortage of materials also prevented
mass-production of the SG-41. It is estimated
that at most 1500 SG-41 machines had been
produced by the end of the war, and most of them
were destroyed in the final days of war to
prevent the technology from falling into enemy
hands, making it now a very rare machine. [1] [2] [3] |
| 1942 |
|
Enigma M4 |
In 1942, the German
Kriegsmarine introduced the notorious Enigma M4.
The M4 had four instead of three rotors, but the
fourth rotor could not step since the stepping
mechanism was identical to the three-rotor
version. After an initial ten months blackout the
British codebreakers in Bletchley Park succeeded
in breaking into the M4 message traffic, codename
SHARK, thanks to cryptanalysis of the fourth
rotor and the capturing of codebooks and weather
codes that were used as cribs. [1] [2] [Simulator] |
| 1943 |
|

M-228 |
The M-228 SIGCUM was
developed by the US as attachment for a
teleprinter. The system produced a pseudorandom
sequence of five bits which were XORed with the
teleprinter signal. To produce the sequence the
SIGCUM used a bank of five rotors with 26
contacts each. Thirteen of the inputs passed
through the rotors to be scrambled and result in
a five-signal output. The rotors stepped just
like an odometer, but which rotor was the fast
one, and which the slower ones was controlled by
switches. Once in service the machine showed some
cryptographic flaws and was withdrawn
immediately. After some revisions it was brought
back into service until the 1960's. [1] [2] |
| 1944 |
|

CCM |
To enable
communications between the Allied Forces in WW2
and later NATO, the US developed the CCM,
Combined Cipher Machine. Adaptors were developed
to make the CCM interoperable with both the US
SIGABA and the British TYPEX. There are reports
about security problems with the encryption
system used and that some rotor combinations had
dangerously short cycle periods. CCM proved to be
a very expensive program. [1] [2] |
| 1947 |
|

NEMA |
In 1941, after the
commercial Enigma was broken, Swiss
mathematicians started working on a new and more
secure design. In 1944 the first prototypes were
ready and in 1947 the NEMA or Neue Machine (new
machine) came into service. Although basically
very similar to the Enigma, the NEMA had ten
rotors, of which four were wired to scramble the
signals and one was used as reflector. The other
five rotors were used to control the stepping of
these rotors. [1] [2] [3] |
| 1950 |
|

PORTEX |
The Portex BID/50/1 is
a rotor cipher machine with eigh 26-pins rotors
that step irregular, similar to the Zahlwerk
Enigma. On the left side is an alphabet wheel to
set the plain or cipher letter. On the right side
a crank to process the letter. During the cycle,
the signal passed through the eight rotors and
the enciphered or deciphered letter is printed on
a gummed paper strip. The Portex was used by the
British Secret Service and the Canadian Army.[1] [2] |
| 1952 |
|

BC-52 |
After the low-level
encryption C-38 and M-209 Hagelin decided to
develop a system that would be usable for high
level military and diplomatic encryption. In 1952
the Hagelin C-52 came on the market. Several
improvements were introduced in the 52 model. The
rotation of the pin-wheels became irregular and
depended on the pin positions of the previous
wheels and for the 6 wheel model there was now
the choice between 12 pin-wheels. Also, the
number of slide-bars was increased to 32. A
slightly different machine was the CX-52. A
separate keyboard attachment was available under
the name B-52. The combination of machine and
keyboard was designated BC-52. Some versions had
a punched tape reader or had only number keys.
This very popular machine was sold all over the
world and was widely used until the 1990's. [1] [2] [3] [4] [Simulator] |
| 1953 |
|
KL-7 |
The TSEC/KL7 is a true
Cold War icon, developed in the late 1940s, and
in 1953 initially introduced under the name
AFSAM-7 by the American National Security Agency
(NSA) as a replacement for the SIGABA. The KL-7
was used by the U.S. Army, Air Force and Navy,
the FBI and CIA, and all NATO countries. The
machine remained in service until 1983. The KL-7
was the first crypto machine to use electronic
components and vacuum tubes, had eight rotors of
which seven rotors moved in a most complex
manner. The rotors had an interchangeable plastic
outer ring with cams, and the movement of the
rotors was electrically controlled by small
switches, operated by the cams on the rings. The
output of the KL-7 was printed on a paper strip. [1] [2] [3] [KL-7 Simulator]
|
| 1955 |
|

CD-55 |
At the request of the
French Gendarmerie, Hagelin developed a small
pocket device with the name CD-55. Two years
later, the CD-57 was manufactured. Input and
output consisted of a ring with an alphabet and a
rotatable disc inside. The alphabet was displaced
by pressing a lever with the thumb. The
displacement depended on the setup of 6 small
pin-wheels, similar to those used in the C Type
machines. About 12,000 of these pocket models
were sold to different countries. [1] [2] [3] [4] |
| 1960 |
|

SINGLET |
The BID/60 SINGLET is a
British machine, used by the Intelligence
services. The SINGLET was based on the same
cryptographic principle as the AFSAM-7 and its
rotors were identical to those of the AFSAM-7,
but the SINGLET was not expected to be in
production before 1960. Until then, the NSA made
available 3,500 units of the AFSAM-7 to the
United Kingdom in 1954. These machines were on
loan and remained property of the NSA. [1 Development KL-7 and SINGLET] [2] [3] |
OMI |
The OMI Cryptograph CR
Mk II is an Italian electromechanical rotor
cipher machine, developed by the firm Ottico
Meccanica Italiano. The OMI has seven 26-pins
rotors, of which one is the reflector. Each rotor
could be assembled from different wirings and
rings with notches. The plaintext and ciphertext
were printed on a double print drum. The CR Mk II
was based on its 1939 predecessor Alpha, and the
1950s Criptograph and Cryptograph-CR. The CR Mk
II was used by the Italian Navy. [1] |
| 1963 |
|

HX-63 |
The only
electromechanical rotor machine, produced by
Hagelin, was the advanced HX-63. The HX-63 had 9
rotors with 41 circuits, of which the surplus
wires were looped back on the outside (somewhat
similar to the KL-7). All circuits could be
rearranged, and the rotors performed irregular
movements similar to the pinwheels on the C-52
series. All this provided an incredible key space
of 10600. Production of the HX-63 was
abandoned due to the development of fully
electronic cipher machines. Only twelve of these
machines are known to have been manufactured. [1] [2] [3] [4] |
| 1965 |
|

Fialka |
The Russian Fialka
M-125 was another well-known Cold War machine.
Developed in the 1950's, the machine came into
service in the Soviet Forces in 1965. Although
based on the Enigma, Russian cryptologists were
well aware of the security flaws of that machine,
and incorporated solutions to all of those flaws
into this wonderful piece of mechanics. The
Fialka had ten 30-pins rotors that stepped in
opposite directions. Each rotor could be composed
from different wiring cores and rings that
controlled their stepping. The plugboard was
replaced by a punched card reader and a 'magic'
circuit in the reflector solved the Enigma's flaw
that a letter could never be encrypted into
itself. The Fialka was top secret until the
1990's. [1] [2] [3] [4] [5] [6] |
| 1970 - 1990 |
|

H460
|
The rise of electronics
in the 1970's lead to smaller and cheaper
electronic machines and the electromechanical
versions could not compete with them. Although
the electromechanical machines still remained in
use for many years they would gradually be
replaced by newer and sophisticated electronics
and cryptographic software on computers.
Hagelin's H-460 was one of the first new
generation machines with fully electronic
generated key. [1] [2] [3] |

Gretacoder 805 |
The Gretacoder was one
of the first compact microprocessor-based cipher
systems, developed by Edgar Gretener for the firm
Gretag. The machine had a 4000 characters memory
and a 37 characters wide display. The Gretacoder
805 system was highly modular and could be
configured as briefcase version, mounted in a
standard briefcace that included a little
printer, or as office setup, including a printer,
paper tape puncher and reader. The [1] [2] |

HC-520 |
The Hagelin HC-520 was
a pocket size cipher machine with LCD display. It
can be seen as an electronic CD-57, but with a
more complex encryption. There were several
different versions of which one was mounted
together with a printer in a Samsonite briefcase.
The HC-520 was in production until 1979. [1] [2] |

KL-51 RACE |
NSA developed the KL-51
in the 1980's. The KL-51 is a fully electronic
ruggedized cipher machine. Key entering was done
by reading in a punched paper tape and it had a
20 letter display for message editing. The KL-51
was designated codename RACE by Canada and NATO. [1] [2] [3] |

MK-85C |
At the end of the
1980's, the Soviet Union developed the
ELEKTRONIKA MK-85, its most advanced commercial
calculator ever to be in production (the MK- 9x
series are prototypes or limited production). The
MK-85 was a programmable CMOS BASIC
microcomputer, based on the western BASIC
machines. The top secret military MK-85C with
codename AZIMUT was based on the commercial
MK-85. It is mainly used by the Soviet Forces.
The text for ciphering is entered from the
alphanumeric keyboard and can be edited on its
matrix display. The MK-85C has 10100
key variations and encrypts in both numeric and
alphanumeric mode. [1] [2] [3] [4] |
| CURRENT |
|
 |
The small handheld
crypto devices can be seen as the last real
stand-alone versions. In today's computer era,
all firms shifted their focus to encryption
software or proprietary cryptographic chips,
imbedded in computers, phones, on-line or
wireless equipment for text, data and voice
encryption. Nonetheless, dedicated pocked-sized
digital equipment is still developed for special
purposes. Most of the old cipher machines are now
hot collector items. More information on recent
equipment is found on the Crypto Museum website:Data encryption , voice encryption , voice encryption , crypto phones , crypto phones , pocket-sized
devices , pocket-sized
devices ,
modern
cryptographic algorithms ,
modern
cryptographic algorithms
|
| |
|